Middle East security
-
System Disruption as Strategy: Trump’s Infrastructure Warfare on Iran

The Evolution of Targeting in the Iran Campaign From Military Objectives to Civil Networks A strike on the B1 Bridge along the Tehran-Karaj northern bypass marks a documented expansion of targeting into civilian infrastructure with no established military function. The structure formed part of a major urban transport project designed to ease congestion across a… Continue reading
AI and Digital Control, China, economics, Energy, EUROPE, Financial markets, Foreign Policy, Geopolitics, Global Finance, iran, israel, NATO, politics, warAdditional Protocol I, airstrikes, civilian infrastructure, conflict analysis, distinction principle, economic pressure, education systems, energy systems, Geneva Conventions, Gulf States, infrastructure warfare, international humanitarian law, iran, israel, Karaj, kinetic operations, legal exposure, medical networks, Middle East security, military targeting, national security, proportionality, resilience analysis, state capacity, strategic escalation, Syrian Civil War, systemic degradation, Tehran, transport infrastructure, war crimes risk -
Ukraine’s Gulf Expansion Tested by Reported Strike in UAE

A reported attack on a drone defense site in the Gulf points to a widening, interconnected conflict landscape Recent developments spanning the Middle East and Eastern Europe point to a potentially significant shift in how contemporary conflicts are structured, extending beyond geographically contained wars into interconnected theatres shaped by shared capabilities, strategic signaling, and alliance… Continue reading
AI and Digital Control, America, China, Energy, EUROPE, Financial markets, Foreign Policy, Geopolitics, Global Finance, iran, israel, middle east, Mineral Resources, NATO, politics, reserve currency, Russia, warair defense, counter-drone systems, defense cooperation, deterrence, Drone Warfare, Game Theory, Geopolitics, global conflict, Gulf States, iran, Islamic Revolutionary Guard Corps, Middle East security, military strategy, military technology, proxy conflict, Qatar, Saudi Arabia, UAV, ukraine, United Arab Emirates, Volodymyr Zelenskyy -
Iran’s “Famous Bride” Jibe as Ghalibaf Mocks U.S. Carrier Departure as Strategic Retreat
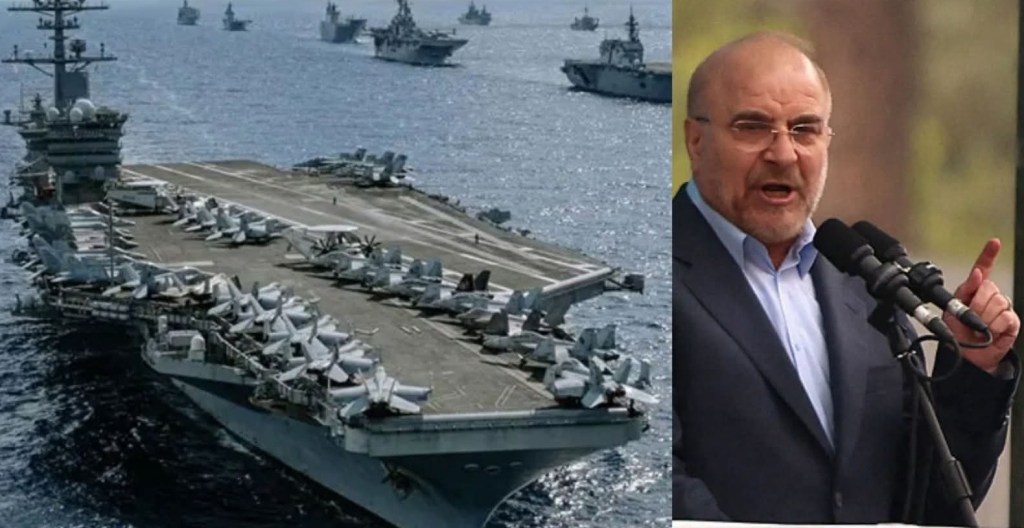
Beyond insult, the remark reflects Iran’s strategy of promoting missile and drone capabilities as tools to deter American power. Iranian Parliament Speaker Mohammad Bagher Ghalibaf used unusually cutting rhetoric to mock the United States over the departure of the aircraft carrier USS Abraham Lincoln (CVN-72), framing the move as proof that American military pressure against… Continue reading
-
Shock Doctrine Decapitation or Deterrence

Washington’s pursuit of rapid decapitation confronts Tehran’s doctrine of attritional survival March 1, 2026 marked the second day of renewed United States military operations against the Islamic Republic of Iran, described by observers as either a new war of aggression or the continuation of hostilities initiated during the previous year. Early operational reporting indicated that… Continue reading
AI and Digital Control, Financial markets, Foreign Policy, Geopolitics, Global Finance, Health, israel, Latin America, middle east, NATO, politics, Russia, warairpower strategy, asymmetric warfare, attrition warfare, ballistic missiles, Clausewitz, decapitation strategy, Drone Warfare, Escalation dynamics, iran, Islamic Revolutionary Guard Corps, Middle East security, military doctrine, mosaic defence doctrine, political economy of war, regime change, sanctions resilience, strategic endurance, Sun Tzu, United States, war of aggression -
Washington Drops the Mask and Calls for Informants Inside Iran

Iranian Leadership Casts CIA Recruitment Appeal as Proof of Regime Destabilization Efforts In a move that dispenses with even the pretense of neutrality, the CIA’s verified X account publicly issued a Persian-language appeal urging Iranians to contact the agency through secure channels, promising it can “hear your voice.” The message included instructions on using Tor… Continue reading
